solutions
Zadyn Group delivers a wide verity of technology solutions to small and large organizations across multiple verticals in Canada and the United States. Our team can Advise, Design, Install and Support the selection of your technology solutions.
The pressure from digital transformation initiatives has fundamentally shifted how companies develop, implement, and manage application environments.
Transform the way you delivery internet and web security.
Secure your business with a prevention-focused architecture and integrated innovations that are easy to deploy and use.
Embraces a zero-trust security strategy for your internal applications.
FIDO is developed by the FIDO Alliance, a non-profit organization that seeks to standardize authentication at the client and protocol layers.
Decentralized Authentication Platform designed to eliminate credential reuse, fraud and phishing for consumers and employees across the enterprise.
Unified Privileged Access Management Solutions that Reduce Insider Risks and Improve Productivity
A Software-defined Wide Area Network (SD-WAN) is a virtual WAN architecture that allows enterprises to leverage any combination of transport services – including MPLS, LTE and broadband internet services – to securely connect users to applications.
Shifting to a business first networking model.
Organizations deploying cloud applications like Office 365, the old approach to routing traffic — backhauling over MPLS to a centralized Internet gateway via a hub-and-spoke architecture is inadequate. To deliver a fast user experience and support cloud applications and services, Internet traffic must be routed locally.
Reduce spend and maintain license compliance wtih enterprise software license management.
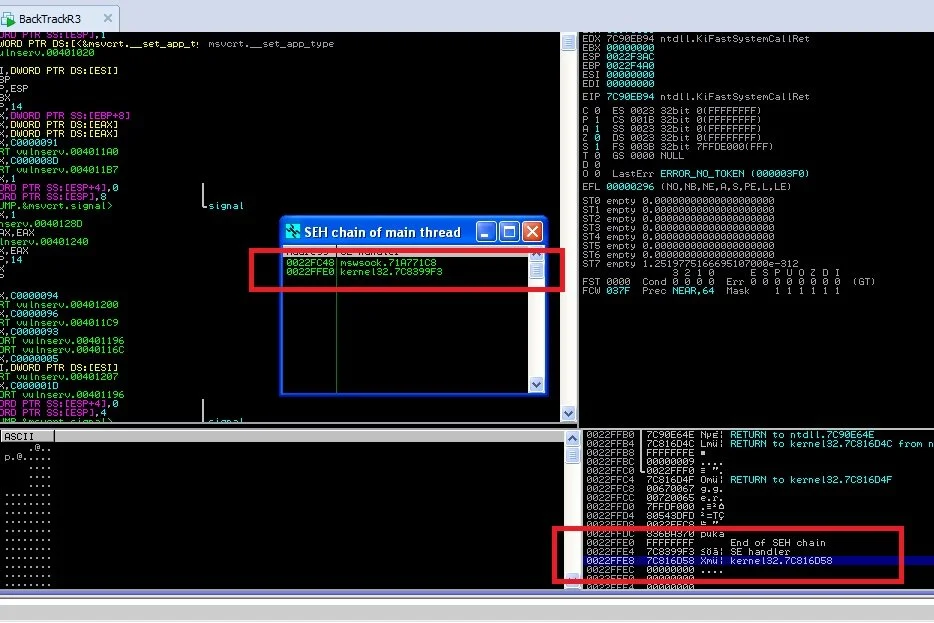
A universal vulnerability exists on your website that prevents you from controlling customer and payment data and provides hackers with unlimited access to website and customer data
Prioritized remediation process by handling vulnerability workflows, tickets and alerts, and describes the steps to mitigate the risk of costly breaches.